Pros and Cons of the Zero Trust Framework
The Zero Trust Framework is essentially what it’s name states. It’s based on not trusting anyone or anything. Using this framework, organisations should not trust any user, application, process or data source regardless of where it is coming from. Anything that is trying to connect to the network or database, requires verification before it can receive access. So anything trying to connect or enter the network is seen as a threat until it can prove itself trustworthy.
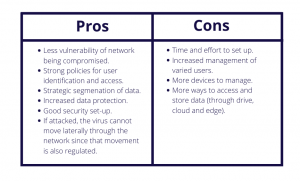
Benefits to the Zero Trust Framework is that it reduces an organisations vulnerability to having its system compromised. In the event that an organisation is victim to a cyber-attack, the virus cannot move throughout the network as each section of the network is regulated by Zero Trust.
Another benefit is that it is a strong policy for user identification and access. Users are not able to get into the network without verification. This is a great way to regulate everyone and everything gaining access to your network. The framework also provides organisations with increase data protection and is a smart way to segment data.
Cons of the Zero Trust Framework is that it takes time and effort to set up. Often organisations build a new network rather than reorganise their existing network, and transfer to the new Zero Trust one. There is also an increased management of users and more devices to manage. This makes it a little more complication to manage, as there is a large number of requests to access the network.
The Zero Trust Framework can be a very effective cyber security strategy. As everyone entering the network needs to be verified, making it more difficult for a networks system to be compromised. The most difficult part of this framework is the set up, and how to transfer your organisation to this new network.
References:
Arntz, P 2020, Explained: the strengths and weaknesses of the Zero Trust model, Malwarebytes, viewed 2nd February 2021,<https://blog.malwarebytes.com/explained/2020/01/explained-the-strengths-and-weaknesses-of-the-zero-trust-model/>.
Canner, B 2019, What is Zero Trust Identity Security? How can you implement it?, Solutions Review, viewed 2nd of February 2021,<https://solutionsreview.com/identity-management/what-is-zero-trust-identity-security-how-can-you-implement-it/#:~:text=Zero%20Trust%20Identity%20Security%20states%20anything%20connecting%20to,as%20untrusted%20until%20it%20can%20absolutely%20prove%20otherwise.>.
Tucker K.K, 2020, Pros and Cons of the Zero Trust Model, Infused Innovation, viewed 2nd of February 2021,<https://www.infusedinnovations.com/blog/secure-intelligent-workplace/pros-and-cons-of-the-zero-trust-model#:~:text=As%20you%20can%20see,%20the%20cons%20of%20using,Without%20assumed%20trustworthiness,%20the%20network%20is%20more%20secure.>.




